Teorias
T1
Software Engineering
Systematic, disciplined, quantifiable approach to the analysis and design, implementation and exploitation of software systems.
T2
Requirements
- expressions of users' necessities and restrictions that are placed on the system;
- for an engineer: something that needs to be conceived;
- a condition or a capacity that someone needs to solve a problem or to achieve an objective;
- a condition or a capacity that must be verified or possessed by a system or by a system component to satisfy a contract, standard, specification, or other formally imposed documents;
- a documented representation of a condition or capacity, as in (3.) or (4.)
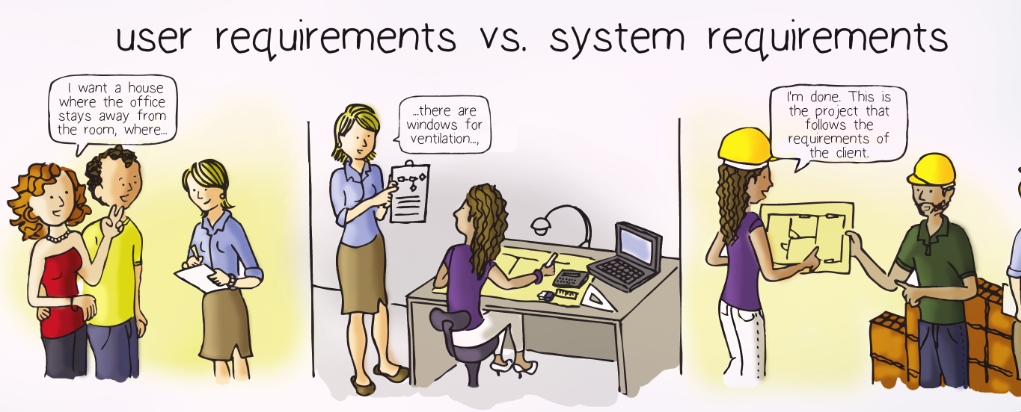
The IEEE 610.12-1990 standard definition divides requirements into two alternatives:
- user needs (user requirements)
- system capacities (system requirements)
Requirements can be divided into:
- functional requirements
- non-functional requirements
A requirement that for a stakeholder can be perceived as being functional, can be considered as non-functional for a different one.
A candidate requirement is a requirement that was identified by some elicitation technique. The use of the term ‘candidate’ aims to emphasise the possibility of the requirement not being considered.
Functional Requirements
A functional requirement describes a functionality to be made available to the users of the system.
- It characterises partially the system behaviour as an answer to the stimulus that it is subject to.
- This type of requirements should not mention any technological issue.
- Ideally, functional requirements must be independent of design and implementation aspects.
Set of Requirements
Collectively, the set of functional requirements must be complete (if it considers all the necessities that the client wishes to see satisfied) and coherent (if there are no contradictions among its elements).
Defining complete requirements is the most difficult attribute to achieve or evaluate.
Implicit and Explicit Requirements
A requirement included by the development team, based on the domain knowledge that it possesses, in spite of not having been explicitly requested by the stakeholders.
A requirement that was requested by the clients and that is represented in the documentation.
Non-Functional Requirements
- a set of restrictions imposed on the system to be developed;
- requirements that establish how attractive, fast, or reliable the system is;
- includes time constraints, restrictions in the development process, or adoption of standards.
"The product must be developed in C++;"
Also refered as quality requirement or quality attribute.
- A non-functional requirement does not change the essence of the system functionalities (AKA the colour of the ball does not affect its functionality).
- Non-functional requirements are applicable to the system as a whole and not just to some of its parts.
- Generally, non-functional requirements cannot be modularised.
- The non-functional requirements are frequently emergent properties of the system at hand.
- An emergent property of a system is a property that can be associated with the system as a whole, but not individually to each of its components.
- Reliability is a good example of an emergent property. It is not sufficient that all components are reliable, for the respective system to be also reliable.
- The size of a software application is an example of a property that is not emergent.
- Non-functional requirements are crucial to decide the system architecture.
Classification of Requirements
- product requirements: characterise aspects of the behaviour of the system itself (reliability, performance, efficiency, portability, usability, testability, and readability).
- organisational requirements: come from strategies and procedures established in the context of the manufacturing process of the system or the client organisation (process standards and implementation requirements).
- external requirements: have origin in external factors to the system and the development process (interoperability, legal, and ethical requirements).
- appearance: the aspect and the aesthetics of the system;
- usability: the easiness of utilisation of the system and everything that permits a more friendly user experience;
- performance: aspects of speed, real-time, storage capacity, and execution correction;
- operational: characteristics about what the system must do to work correctly in the environment where it is inserted;
- maintenance and support: attributes that allow the system to be repaired or improved and new functionalities to be added;
- security: issues related to access, confidentiality, protection, and integrity of the data;
- cultural and political: factors related to the stakeholders culture and habits;
- legal: laws that apply to the system so that it can operate.
- Ease of use is related to the efficiency of utilising a system and with the mechanisms that reduce the errors made by the users.
- Personalisation is associated with the capacity of adapting the system to the tastes of the users.
- Ease of learning is concerned with the way users are trained to use the system.
- Accessibility indicates how easy it is to use the system, for people who are somehow physically or mentally disabled.
- System maintenance is divided into four types: preventive, corrective, perfective, and adaptive.
- Modifiability is related to maintenance and is dependent on how easy it is to locate the components that must be changed;
System Requirements
A more detailed specification of a requirement, being generally a formal model of the system. These requirements are oriented towards the solution domain, helping the engineers in the system design and construction.
They are documented in a more technical language than the one adopted for the user requirements. It is desirable that they are independent from design and implementation pre-decisions.
Problem Domain
- The requirements result from necessities that exist in the problem domain to be addressed;
- User requirements should be described with the problem domain terminology.
SUMMARY T2
- Requirements represent the necessities of the users and the constraints that are applied to a system and that must be considered throughout the development.
- The requirements can be classified, according to a first criterion, as either functional or non-functional.
- Non-functional requirements are divided in 8 different types: appearance, usability, performance, operational, maintenance and support, security, cultural and political, and legal.
- The requirements can be designated as either user or system requirements.
- User requirements are related to the problem domain and are usually expressed in a natural language.
- A system requirement is oriented towards the solution domain and is a detailed specification of a requirement, generally in the form of a formal model of the system.
T3
Requirements Engineering
- All the activities related to requirements discovery, negotiation, documentation, and maintenance; Alternative designation: analysis.
- The study of a problem that leads to the system development, before taking any design or implementation action.
- Requirements engineering, in the scope of software engineering, is focused on the real-world objectives established for the functionalities and the restrictions of software systems.
- The process of discovery, analysis, documentation and checking the services and restrictions related to the operation and development of software systems;
- A set of structured activities that, with respect to a system, aid in obtaining an understanding about the domain, the restrictions of operation, the functionalities requested by the stakeholders and the essential characteristics.
- Requirements Engineering is related to the transformation of informal descriptions of the real world into specifications in languages with a rigorous basis.
- Its objective is to increase the chances of the system under development to satisfy the future.
- Requirements engineering seeks to ensure the three following objectives:
- all the relevant requirements are explicitly known and comprehended at the intended level of detail;
- a reasonable and wide agreement about the requirements is obtained among the stakeholders;
- all the requirements are duly documented, in conformity with the established formats and templates
- Requirements engineering determines what the system must do to meet the necessities of users and not how it should be built.
- It is desirable keeping the requirements strictly separated from their own solutions.
The requirements of a given system are necessary, clear, correct, complete, viable, traceable, verifiable and negotiable.
Requirements Engineering Process
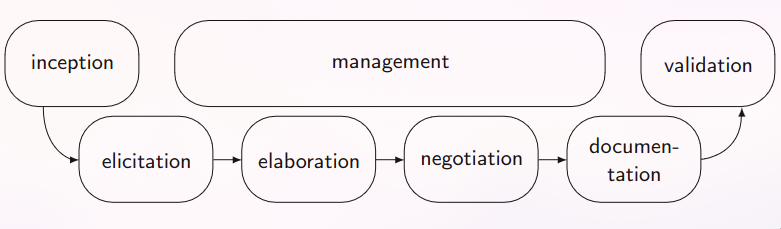
- The phases of Elicitation, Negotiation and Documentation lead to specifications, documents, artefacts and models;
1. Inception
- Based on some necessity or business expectation (usually due to the dissatisfaction in relation to the current situation)
- This recollection must be done in width and not in depth.
- At the end, the requirements engineer should be able to describe what is the client vision and return on investment (one must evaluate if what the client needs is already available in the market. If not, it must be created).
2. Elicitation
- Requirements elicitation techniques must:
- identify the sources of requirements;
- aid the various stakeholders to correctly describe the requirements.
- Inherently communicational: requires an in-depth interaction with the stakeholders
- Techniques:
- interview
- survey
- introspection
- ethnography
- focus group
- cooperative work
- domain analysis
- object-orientation
- prototyping
- scenario
- goal modelling
- persona
3. Elaboration
- usually to organise the requirements in cohesive groups
- The analyst must intervene, whenever the requirements:
- do not make sense;
- are in contradiction among them;
- are incoherent;
- are incomplete;
- are vague.
4. Negotiation
- involves communication and negotiation
- Results can have a significative impact on the acceptance of the final system.
- Another form of handling conflicts consists in adopting prioritisation techniques, to sustain the choice of the requirements subset to be implemented at each instant.
5. Documentation
- Requirements documents serve as the principal reference to the subsequent phases
- The requirements document is organised according to two distinct perspectives:
- user requirements, that describe the expectations and the necessities of the users;
- system requirements, that establish the agreement between the client and the development team.
- The structure/formality of the documentation should vary in line with the system characteristics and the adopted process
6. Validation
- The objective is to ensure that the requirements define the system desired by the client.
- One should examine the requirements document through inspections or technical reviews of the specifications, to evaluate if it describes the intended system.
- Validation is a testing activity.
7. Management
- The requirements set is constantly changing.
- Mechanisms to manage that instability context are needed, in order to evaluate the impact that the changes can have on the project.
- The requirements management activity seeks to aid the development team to identify, control and trace the requirements and their changes.
- there would be a significative increase in cost;
- there would be a postponement of the final delivery;
- there would a system devaluation for the user (system gets worse from a user stand-point).
Dimensions of Requirements Engineering
What is our objective? How to get there (make documents more vague or more formal...)?

Dificulties of Requirements Engineering
- Communication problems between requirements engineers and users are common.
- Professional Jargon - aka technical speak that nobody else (stakeholders) understands
- Clients unable to verbalise what they desire
- Solved by observing the users performing their functions in the real context
- Clients do not notice that they explained incorrectly the problem until they receive a solution that does not satisfactorily solve it
- Solved by making sure that, prior to starting the development, the problem to be handled is well formulated and corresponds to the reality (AKA communicate with the client and ask specific questions about what they need)
- The engineer thinks he knows more about the problem of the client than the client himself
- Solved by making sure the engineer feel the difficulties faced by the users in the real context (AKA put yourself in the shoes of the client)
- Frequent changes of requirements
- changes in the requirements must be considered as a natural fact and not as the result of an initial request poorly formulated
- Solved by finding adequate mechanisms that allow changes in the requirements to be incorporated, without major perturbations in the work previously developed and the development team being adequately prepared to cope with the various changes
- Requirements engineering is one of the most difficult activities to be executed in the scope of software engineering
- No technique used in isolation is sufficient to elicit the requirements of a system
- Requirements engineers must select the techniques that are appropriate to the complexity of the system and to the development context
SUMMARY T3
- Requirements engineering aims to establish communication channels between the problem holders and those that will build the solution.
- The requirements engineering process includes seven main activities: (1) inception, (2) elicitation, (3) elaboration, (4) negotiation, (5) documentation, (6) validation, and (7) management.
- Requirements engineering allows the functionalities and the restrictions of the system to be elicited, negotiated, and documented.
- The clear definition of the requirements has a decisive influence on the quality and utility of the final system.
- After discussing the problem, interviews and discussions with the stakeholders should be organised.
- A project hardly constitutes a success, if all stakeholders do not provide their opinion w.r.t. the requirements.
T3
Template for Requirements Documents
The definition of a generic template for the documents that specify the requirements is an important aspect, since there is a great diversity of engineering systems and projects. Without ir, the degrees of freedom are excessive, making the documents quite different from case to case.
- Project Triggers
- purpose of the system
- client, customer, stakeholders
- users of the system
- Restrictions of the project
- mandatory restrictions
- taxonomy and definitions
- facts and assumptions
- Functional requirements
- scope of the work
- scope of the system
- functional and data requirements
- Non-functional requirements
- appearance
- usability
- performance
- operational
- maintenance
- security
- cultural and political
- legal
- Project issues
- open issues
- immediate solutions
- new problems
- tasks
- migration to the new system
- risks
- costs
- user manual
- waiting room
- ideas for solutions
Guidelines for writing requirements documents
- Writing requirements in a natural language is inescapable.
- Engineers must be able to write requirements in a natural language and, in general, must know how to communicate with any common person (no jargon).
- Writing in an effective way is a task prone to errors.
- Writing requirements, according to a set of principles and recommendations, is important, making it a process with continuous enhancement, through training and practice
Advantages:
- there are no limits to expressiveness
- it is understandable by all literate persons
- it does not require any specific training.
Disadvantages:
- Free writing presents normally many ambiguities.
- The final quality varies from case to case.
- The language must be simple, clear, and precise.
- No figures of speech, like metaphors or similes
- The words should be adopted in their denotative meanings, aka no space for possible alternative interpretations
- Technical writing must be done in an impersonal, objective, clear, humble, and polite style.
Standardized format for user requirements
- a subject that indicates the type of users that benefit from that requirement;
- an intended result to achieve with the requirement (using a predicate):
-verb (i.e., functionality to be performed)
-other sentence elements to complete the predicate: (direct, indirect, prepositional) objects, predicatives, and adjuncts
- a mechanism to allow a test for the requirement to be defined
user - The hotel receptionist
functionality - should visualise
object/concept - the room number of a guest
test - 2 seconds after making the request.
User Stories
A simple and short description of a functionality, made in the perspective of the person that needs it.
As a <\type of user>, I want to <\objective> for <\reason>.
As a hotel receptionist, I want to visualise the room number of a guest for calling him if someone wants to contact him.
Standardized format for system requirements
- A subject, either the system under development or a design entity that is related to the requirement.
- an intended result to achieve with the requirement (using a predicate):
-verb (i.e., functionality to bring about)
-other sentence elements to complete the predicate: (direct, indirect, prepositional) objects, predicatives, and adjuncts.
system/entity - The signal of the battery
functionality - must turn on
description - when the charge is lower than 20 mA h
Standardized format for non-functional requirements
- the system under development or a design entity that is related to the
requirement. - a quality to be achieved with the requirement:
-verb (in some cases, a verbal form of “to be” or “to have”, or something equivalent);
-object (i.e., a description)
- The product shall be easy to use for illiterate persons
- The product must continue to function at 30 metres under water.
- The product must be prepared to be translated to any language.
- The source code of the product programs should contain comments
How to write requirements
- Each requirement must be represented by one sentence and each sentence should just represent one requirement. The objective is to have the requirements written clearly and this presupposes short and simple sentences.
- The sentences must be affirmative and written in the active voice. Avoid negative and passive voice.
- References to other documents should be limited, especially those with restricted and limited access.
Possible problems with writing
- Avoid the use of terms that may create confusion, especially synonyms of words that represent important concepts.
- Acronyms and abbreviations must be used with great care.
- Avoid using synonyms just to make the text less repetitive.
- Ambiguity means that there are two or more possible interpretations for a sentence
- Situations of ambiguity must be corrected, with the objective of making a sentence clearer
- Ambiguous sentences can be complemented with other materials (tables, figures, schemes), to make the meaning clearer.
- Ambiguity is manifested also when two or more conflicting requirements are defined.
- The resolution for ambiguity can be solved through negotiation techniques.
- Examples of vague terminology: easy to use/learn, versatile, flexible, intuitive, modern, improved, efficient, approximately, more possible, minimal impact...
- Vagueness can be mitigated by complementing the writing of the requirement with the definition of verifiable criteria (AKA use units of measurement)
- To solve delusion, one should avoid any sort of wishful thinking, in which one is trying to reach the impossible.
- Have a realistic attitude. Avoid these therms: 100% reliable, totally safe, never fails, satisfies all users, handle all unforeseen situations...
- Requirements that contain coordinating conjunctions are especially susceptible to create ambiguity situations (in reality we have 2 requirements and not 1).
- Avoid using of coordinators like: for, and, nor, but, or, yet, so,...
- To solve multiplicity divide one requirement into simpler ones.
- Avoid indicating how the system will be able to satisfy a given requirement. There is such a thing as detailing too much a requirement and making design decisions too prematurely;
- Focus of the writing process on functionalities;
- References to component names, materials, database fields, or technological aspects should be avoided;
- Project plans and the way the project is scheduled are important aspects to consider, thus they should not be included in the requirements document;
- Avoid the inclusion of dates, phases and project activities in the requirements. That type of information must be available in a different document - project plan.
Ambiguity
Words, expressions, or sentences that express more than one possible understanding.
It should be avoided in requirements writing, since all technical documents must be clear.
- Homonymy: occurs when two or more distinct and unrelated meanings accidentally share the same lexical form.
- Polysemy: occurs when the same lexical unit supports two or more distinct meanings, but somehow semantically related.
- Use of possessive pronouns: imprecise uses of possessive pronouns in the third person (in the singular or plural) can create ambiguity. Example: The director call the doctor about his problems.
- Conjuntions (1): A problem of interpretation exists when, after an enumeration, one writes something that can be applied to all the elements enumerated or just to the last one. Example: The managers inform the directors and the secretaries, because they are responsible for editing the document.
- Conjunctions (2): Also, the difference between the linguistic OR and the logical OR (as well as the AND) are also an issue. Conjuctions should be eliminated whenever possible.
SUMMARY T4
- The use of requirements written in a natural language is common in engineering projects.
- It fosters communication among the various stakeholders.
- Writing is a task prone to errors and problems, since what is written often is interpreted in a different way than intended.
- A set of practical recommendations for writing good requirements in English was described.
- Having the requirements written in a clear and standardised way results in advantages for all participants in a given project.
- The structure of a standard template for documenting requirements, with 27 possible sections, was discussed.
- Ambiguity-related issues in natural languages are discussed.
- Ambiguity happens when there are two or more possible interpretations for a sentence.
- Ambiguity is addressed for highlighting some aspects to be taken into account when writing requirements.
T5
Elicitation
- Requirements elicitation permits to understand what are the requirements of a given system. It allows comprehending the necessities and expectations that stakeholders have with respect to a given system. The activities have a communicational nature, which involves techniques related with the social sciences and organisational theory.
- Alternative designations: requirements discovery, capture, recollection, acquisition, extraction or crawling
Process of Elicitation
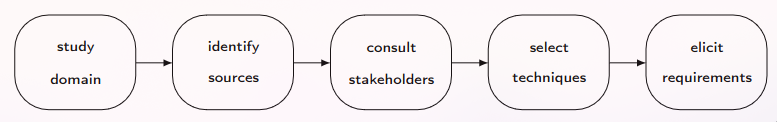
- The activities related to requirements should not be exclusive of the initial phases of the lifecycle.
- The development team must adopt an approach that addresses and favours handling the requirements in all the lifecycle.
- Contact persons that know well the problem to identify all the restrictions that could limit the respective solution ( uncertainty and an increase of information and knowledge)
- Prepare the requirements document that describe the behaviour and the characteristics that are expected for the system (organisation of the ideas, the resolution of conflicting views, and the elimination of inconsistencies and ambiguities)
Stakeholders
Some person (meaning: person/group of people/organization) that has some type of legitimate interest (meaning: will be utilising, be affected by, or have some kind of responsibility in relation to) in that system, as they can be materially affected by the implementation of that system.
Roles
- The identification of the various stakeholders can be performed through the characterisation of the roles or positions that exist in the organisation.
- Some persons can accumulate several roles
- Example: the director of a company that is also responsible for financial accounting
Ways for identifying roles
- Ask the client;
- Examine the organisation chart;
- Compare with similar products;
- Analyse the system context;
- Consult the stakeholders that are commonly found in the majority of the systems
Users
Any person that operates and interacts directly with the system, whenever it is in effective operation in its environment.
The driver and passengers of a car are users, despite their distinct responsibilities.
- One should give preference to the users that more frequently interact with the system.
It is recommended to collect informations to understand if there is any particularity to be recorded for some of the following groups of persons, while they interact with the system:
- disabled and handicapped persons;
- people with low literacy levels;
- those that do not dominate the languages used by the system;
- people with visual difficulties (users of glasses, colour-blind, or blind people);
- persons transporting or handling substances and objects;
- persons with reduced dexterity to interact with computer-based systems.
Clients
The entity that orders and pays for the development of a system.
- The client should be provided with complete technical documentation, to permit the installation and maintenance of the system throughout its lifecycle.
- The client has the power to decide about several issues, namely the scope, functionalities, and cost.
- The clients are not always the users of the system.
Customers
Someone who pays for acquiring a system, whenever available.
- These are the ultimate consumers, for whom the system is rendered.
- For a mass-market product, the customers are the persons that will acquire that product when available.
- The act of buying does not need to be associated with a financial transaction between the customer and the seller.
Market Segment
The characterisation of the necessities and common behaviours of the customers to which is oriented a given product defines its market segment.
AKA necessities + common behaviours of customers -> create a market segment
Market segments are where products thrive (generate a product which solves the needs of customers and you will gain financially and make many happy customers)
A group of customers represents a distinct market segment if:
- their necessities demand and justify a different offer;
- they are approached through different distribution channels;
- they need different types of relations;
- they have significantly distinct levels of profitability;
- they are willing to pay for different aspects of the offer.
Negative Stakeholders
Someone that desires that the system is not developed.
AKA competition, people with financial/political gain if the system is not developed...
- The identification of the negative stakeholders allows to identify any attempt to sabotage the system development.
- Their presence in the requirements elicitation activities is relevant, to identify and comprehend the personal and political relations within an organisation
General competencies of a requirements engineer
- Questioning: to ask questions about the requirements to the right persons;
- Observing: to witness the behaviour of the users of an existing product, system or process, to infer their necessities;
- Discussing: to argue with the users their necessities, with the aim of formulating an understanding about the requirements;
- Negotiating: to ease the negotiation among the users, to achieve agreed solutions about the requirements to be included, removed, or modified;
- Supposing: to anticipate functionalities that the users may need or desire, especially when new mass-market products are bring created
Groups of techniques of a requirements engineer
- Marketing, where there is a special interest in requirements that contribute to the commercial success of the system;
- Psychology and sociology, emphasising the satisfaction of the necessities of the users, the individuals and social agents;
- Participative design, where there is an active involvement of the users in the definition of the requirements;
- Human factors and human-machine interaction, whose focus is the interaction of the users with the system;
- Quality, in which the principal interest consists in the relation between the requirements and the system quality;
- Formal methods focused on the precision and mathematical rigour of the requirements specification.
Requirements Techniques
| Individual | Groups | Artefacts |
|---|---|---|
| 1. Interview | 5. Group dynamics | 7. Domain analysis |
| 2. Survey | 6. Cooperative work | 8. Object-orientation |
| 3. Introspection | 9. Prototyping | |
| 4. Ethnography | 10. Scenario | |
| 11. Goal modelling | ||
| 12. Personna |
1. Interview
- Great freedom to the conductor of the interview
- Often ends with low-quality results
- Should be carried out in a structured way to get better results
- Process: identify interviewees; prepare interview; conduct interview; conclude interview
- Interviewees should include some stakeholders (the client + some users of the system, bare minimum)
- interviewees must (globally) be a representative sample of the community
- possible to add persons to be interviewed during the process of interviewing ("who shall I also interview?")
- interviewer should put the interview in its context, explaining the aims, duration, issues to be addressed and how the collected information will be processed
- Whenever available, the use case diagrams can be used as a reference; models or figures can be used to encourage the interviewee to propose modifications.
- The terminology of the problem should be used (NO JARGON!)
2. Survey
- Common use to elicit requirements, especially initially
- Uses a questionnaire to handle information gathered from multiple persons
- Process: identify audience + objectives; conceive questionnaire; determine sample; recruit participants; conduct survey
- Questionnaire: set of questions to be answered
- When the same questionnaire is used for all persons, it becomes possible to handle statistically the collected answers.
- Success is highly dependent on the way the questionnaire is conceived.
- If questions are not focused, are poorly formulated or appear in the wrong order, the answers may be misleading
- One should avoid the use of negative questions
- Unanswered questions can be tackled through the use of computer-based tools (virtual forms) -> not always desirable, forces the respondent to have access to a computer
- The survey must be used as a preliminary technique that aids in the preparation of the interviews
3. Introspection
- most basic, obvious, and rudimentary of all requirements elicitation techniques
- The analyst defines the requirements for a given system based on what she thinks are the necessities of the stakeholders, by putting temselves in the role of the client or the users.
- They must reason based on premises of the type “if I were the client, I would like the product to . . .”.
- Extensively used, namely when the requirements engineers have a deep knowledge about the problem domain
- Can be used only as a starting point for the adoption of other requirements elicitation techniques
- Brainstorming eases the generation of ideas.
- A brainstorming session congregates a group of 5 to 12 persons
- The group suggests and explores as many ideas as possible, without criticising or judging those ideas.
- Process: generate ideas; consolidate ideas
7. Domain Analysis
- Analysing documentation and studying existing systems is a good source of requirements
- presupposes analysing the upstream and downstream systems, as well as examining systems with similar purpose
- Obtains a larger knowledge about the problem domain
- The objective is examining the domain in which the system is located, to identify the common elements of all systems in that domain
- Analysing documents is a technique based on searching requirements in documents, reports, and manuals.
- The use of this technique will be possible in the future, if the artefacts for the current projects are stored
9. Prototyping
- Sometimes, the client just defines some generic objectives for the system, not indicating with detail its functioning.
- A prototype-based approach can be the most adequate choice to support the requirements elicitation process.
- This approach assumes an iterative process
- Process: elicit requirements; construct prototype; tets prototype
- The prototype serves simply as a mechanism for capturing the requirements.
- As soon as one considers that the requirements of the client are clearly understood, the prototype is abandoned.
12. Personna
- common in the advertising area and recently has gained popularity for requirements engineering
- A persona is a fictitious person that represents an important type of the users of the product under development.
- A persona is an archetype of the persons that are part of the target audience.
- A persona should be conceived to represent those persons, in what is essential and distinctive.
- The personas are a technique of market segmentation
- Process: identify problem; create personnas; introduce personnas; use personnas; evaluate personnas
SUMMARY T5
- Requirements elicitation involves various activities that allow to identify which are the requirements for a given system.
- The requirements engineering techniques cover essentially the analysis phase.
- Requirements engineers dedicate their efforts to contact the persons that know well the problem:
- to identify all the restrictions that can limit the solution,
- to decide how to organise the requirements document.
- The identification of the stakeholders is an important task.
- A system stakeholder is a person that has some sort of legitimate interest in that system.
- The analyst must dominate a large set of technique and to be able to select and apply those that best adapt to each project.
T6
Models
Modelling is the process of identifying adequate concepts and selecting abstractions to construct a model that appropriately reflects a given universe of discourse.
- Modelling permits the cost-effective use of the model in place of the real-world object or process for some purpose.
- Modelling is related to abstraction, simplification, and formalisation.
- A model represents the reality for a given purpose.
- A model must not represent all aspects of reality.
- Abstraction. A model is a reduced description of the system.
- Understandability. By removing detail that is irrelevant for a given viewpoint, models, if specified in an intuitive way, allows one to more easily understand some of the system properties.
- Accuracy. For the properties of interest, a model provides a true-to-life representation of the system.
- Reasoning. A model helps in correctly analysing and reasoning about the interesting but non-obvious properties of the system, either through experimentation (e.g., by simulating the model on a computer) or some type of formal analysis.
- Inexpensiveness. A model must be drastically cheaper to construct and analyse than the system.
Dimensions of a model
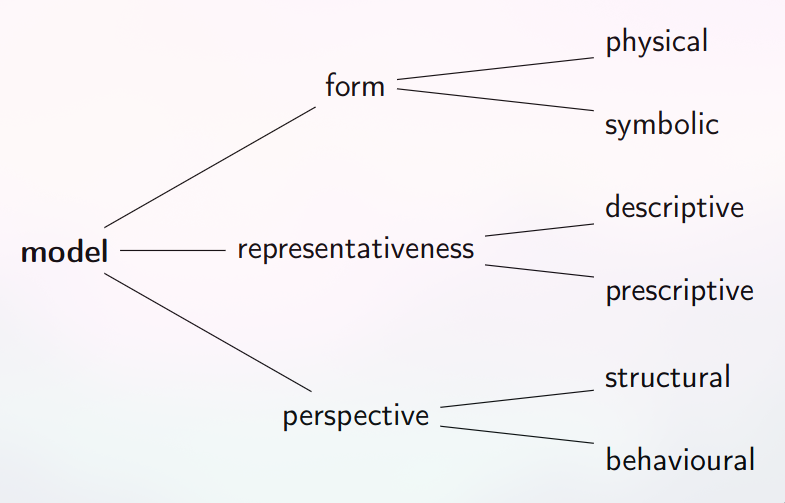
1. Physical/Iconic Models
A reproduction at a reduced scale of a process arising in Nature.
- An iconic model is perceived as imitating the system, being similar with respect to some of its properties.
- A physical model is typically a smaller representation of the original object.
- It can be larger if the original object is too small for humans.
- Usually, a physical model is not as accurate or complete as reality.
- Example: maquetes of buildings
2. Symbolic/Mathematical Models
A model which uses logical and quantitative relationships involving the dimensions of the system.
- In electrical engineering, models are a set of equations that represent the electrical circuits by applying some laws.
- Example: Ohm’s law -> V = R × I .
- Typically, a symbolic model does not resemble the system it represents, but is fundamentally arbitrary or conventional.
- Arbitrariness is the absence of any necessary connection between a linguistic form and its meaning.
- A class is represented in UML by a rectangle, but this is a pure convention. The word ‘strawberry’ has no relation to the fruit itself; it is a pure convention.
- Topological maps are also an example of a symbolic model. Those subway maps as well.
3. Descriptive Models
Models which are used to describe or mimic a real-world phenomenon or system.
- With a descriptive model, one can reason about the properties or the behaviour of the system.
- An example is a model of the weather that allows meteorologists to forecast it.
- In almost all natural sciences, models are descriptive as scientists try to understand how the natural world behaves.
- In engineering, descriptive models are used in reverse engineering when one wants to reason about an existing system without directly affecting it.
- AKA models which are written down descriptions of what we are trying to represent (that exists/is something tangible)
- REVERSE ENGINEERING
4. Prescriptive Models
A model which is used to define how a yet-to-be-built system is supposed to be.
- Prescriptive models are adopted in the so-called forward engineering.
- In software engineering, models created during the analysis stage describe the problem at hand.
- When prescriptive models are used, the target system does not exist yet! It must be engineered.
- Most of the models used in engineering are prescriptive
- FORWARD ENGINEERING
5. Structural Models
A model that is focused on the static aspects of a system.
These models are used for describing the components or modules that are part of the system, so they serve for conceptualising the system architecture.
UML class, component, and deployment diagrams are used for representing structural models.
6. Behavioural Models
A model which emphasises the dynamic, functional, and temporal aspects of the system.
-This type of models address the behaviour of the system, being thus especially relevant in the analysis phase.
Examples: finite state machines, Petri nets, and data flow diagrams (DFDs).
UML Models
- Modelling, done during the analysis phase, aims to specify the requirements of the systems.
- Most software models are, in industrial contexts, represented in UML.
- This language presents many types of diagrams.
- Most developers use in practice only a subset of those diagrams and from those also resort just to part of their available constructors.
- This situation is easily framed in the Pareto law (or 80/20 rule- for many outcomes, roughly 80% of consequences come from 20% of causes (the "vital few")).
| model | purpose |
|---|---|
| domain | describe the vocabulary, concepts of the domain and characteristics of the systems that can be developed for that domain |
| use case | describes the proposed functionalities of a given system |
| interaction | show how the various objects or entities collaborate, emphasising the flow of control and data among them |
| class | present a set of concepts, types and classes and the respective relations |
| state | specify the behaviour of an entity or indicate the various states (or modes) through which it transits throughout its life |
| activity | show the control flow among the activities of a process |
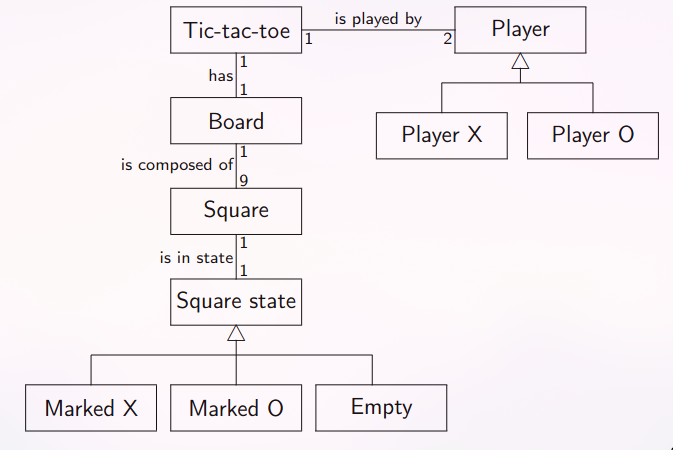
1. Domain model
A domain model is a description of the common properties and variables of the domain related to the system that is being developed.
- The domain model expresses enduring truths about the universe that is relevant to the system at hand.
- That description must include:
- a definition of the 1 of that domain, providing examples of systems or generic rules of inclusion,
- the vocabulary of the domain (i.e., the glossary with the principal terms)
- a model of concepts that identifies and relates the concepts of that domain.
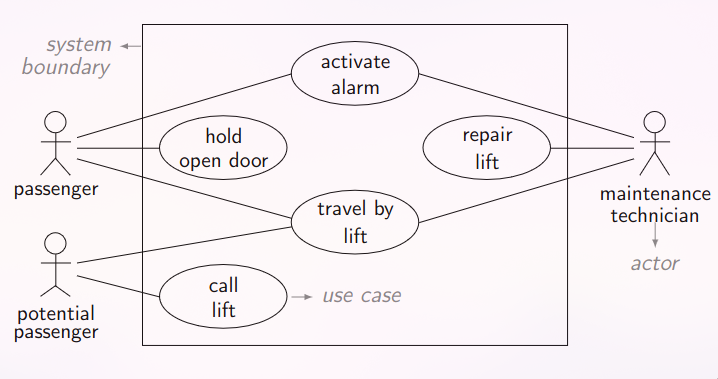
2. Use Case model
- The utilisation of use case models serves essentially two purposes:
- defining the frontier of the system with the environment,
- specifying the functionalities that the system makes available to its users.
- A use case diagram resorts to, as basic elements, use cases and actors.
- The usage of verbs is recommended to characterise the use cases, thus enhancing their functional nature.
- Use cases do not model processes/workflows
- You can use abstractions for actors
- Many small use cases with the same objective may be grouped to form one (more abstract) use case
- The various steps of a use case are not separate use cases themselves! NO functional decomposition
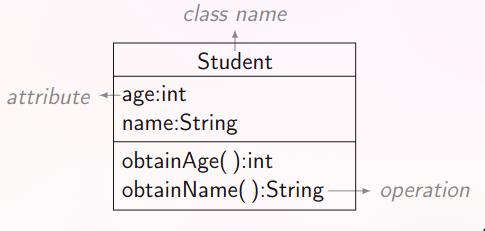
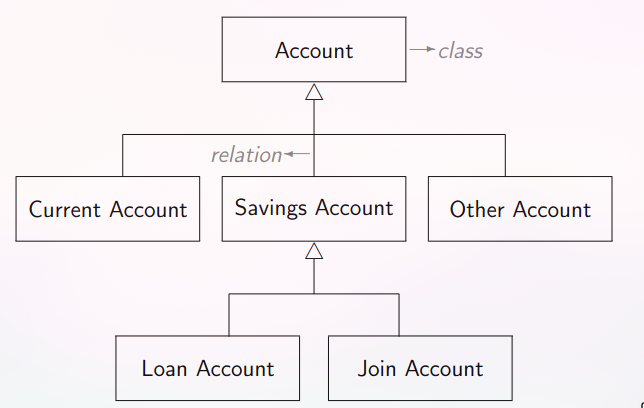
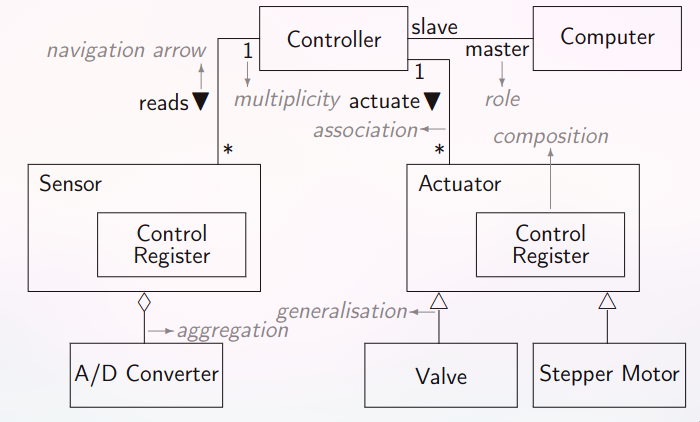
3. Class model
- Class models are necessary to indicate the existing classes and their relations.
- These models are contemplated by all object-oriented software development methods.
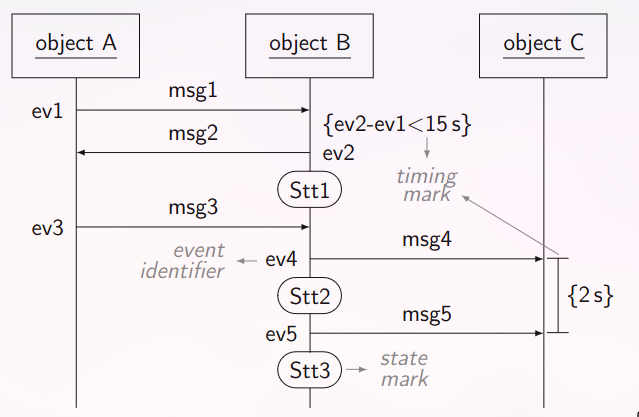
4. Sequence model
- In same cases, it is necessary to model the dynamic aspects related to the exchange of messages between objects.
- Those models can be represented by interaction diagrams.
- An interaction model can be used for representing an instance of a use case.
- They describe how a group of objects communicate amongst them.
- In UML (version 2.2), there are four different types of diagrams that allow interaction models to be represented.
- We present only sequence diagrams.
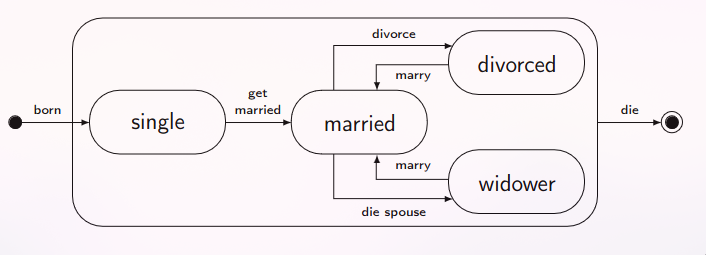
5. State Model
- Class models do not allow the dynamic behaviour of the instances of the classes to be determined.
- The use of state diagrams has become popularised in the hardware domain, but its modelling capacity has proved to be useful in diverse computing areas.
- State diagrams can be used for defining the (dynamic, temporal) behaviour of a class.
- In a conventional state diagram, one and only one state is active in each instant.
- A state is an ontological condition that persists for a significant period of time that is distinguishable and disjoint from other similar conditions.

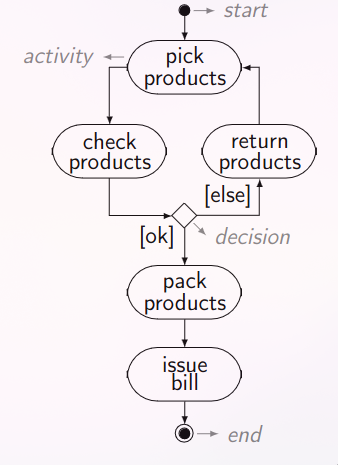
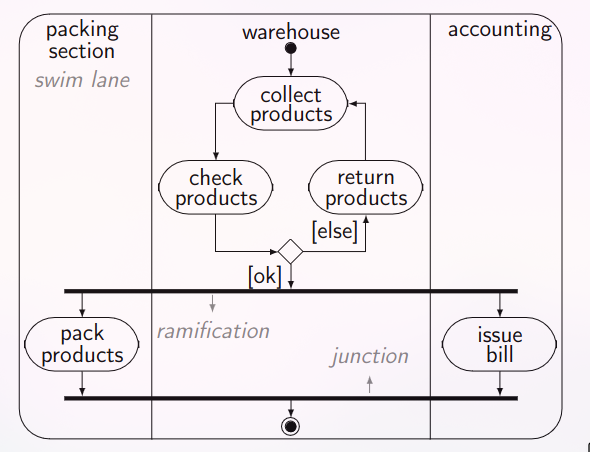
6. Activity Model
- Activity models are useful to relate the control flow among the activities of a given business process.
- These models address behavioural aspects of the systems or entities under consideration.
- These models are appropriate when the behaviour change occurs, mainly due to the end of the action/activity executed
SUMMARY T6
- Using models is essential in all engineering branches.
- A model represents in a simplified way the reality for a given purpose, emphasising some elements and ignoring others.
- The models to be effectively useful, must possess to a sufficient level the following characteristics: abstract, comprehensible, accurate, predictable, and inexpensive.
- Models can be characterised according to three dimensions: form (symbolic, physical), representativeness (prescriptive, descriptive), and perspective (behavioural, structural).
- Some UML models for documenting the requirements of a system were presented.
- For requirements engineering, domain, use case, interaction, class, state, and activity models are deemed crucial
T7
Principles
A principle is a comprehensive and fundamental law, doctrine or assumption. Software design principle are key notions that provide the basis for many approaches/concepts. Such design principles are:
- Abstraction
- Coupling and cohesion
- Decomposition and modularization
- Encapsulation and information hiding
- Separation of interface and implementation
- Sufficiency, completeness and primitiveness
- Separation of concern
Design
The conception or invention of a scheme for turning a specification for computer software into operational software.
- Design is the activity that links requirements to coding and testing.
- A good top-level design provides a structure that can safely contain multiple lower-level designs.
- Good design is indispensable on large projects.
Design Levels
- Software system
- Division into subsystems/packages
- Division into classes with packages
- Division into data and routines within classes
- Internal routine design
Software Architecture
- Set of structures needed to reason about the system, which comprise software elements, relations among them, and properties of both.
- Fundamental organization of a system, embodied in its components, their relationships to each other and the environment, and the principles governing its design and evolution.
- The static structures of a system define its internal design-time elements and their arrangement.
- The dynamic structures of a system define its run-time elements and their interactions.
The fundamental properties of a system manifest in two different ways:
- The externally-visible behaviour defines the functional interactions between the system and its environment
- A quality property is a non-functional property.
- A software architecture is the realization of early design decisions to decompose the system into parts.
- If two architects are given the same requirements, in general, they produce different architectures.
- Functional requirements do not determine architecture.
- stakeholders
- developing organization
- background and experience of the architects
- technical environment
- A software architecture is the result of technical, business and social influences.
- Software architecture is about the design of the system and the impact it has on its qualities.
- The architecture acts as the skeleton of the system, constrains it, and affects its quality attributes.
- Applying software architecture ideas requires a conscious shift to embrace its abstractions.
- If you do not consciously choose the architecture of your systems, then it end up being a big ball of mud (“spaghetti code”) - AKA a software system that lacks a perceivable architecture.
- Every system has an architecture, whether or not it is documented and understood.
Risks
- Each project faces risks, so there is no single correct way to do software architecture
- Often there is no architecture work, since there is no risk when a proven architecture is reused.
- The harder the problem is, the more one needs to pay attention to the architecture choices.
- A software’s design consists of the decisions and intentions that are in the heads of the developers.
- The solution space is small
- The risk of failure is high
- There are difficult quality attribute requirements
- A new domain is being considered
- A software’s design consists of the decisions and intentions that are in the heads of the developers.
Architecture design and detailed design
The design phase can be partitioned into two parts:
- Architecture design is the macroscopic parts of the design, such as modules and how they are connected.
- Detailed design covers everything else.
The output of design is:
- a set of artefacts that record the decisions that were taken
- the rationale for each non-trivial decision is explained
Every system comprises elements and relations among them.
Dependencies
- Each component plays a specific role in the system.
- The components collaborate to provide the required functionality.
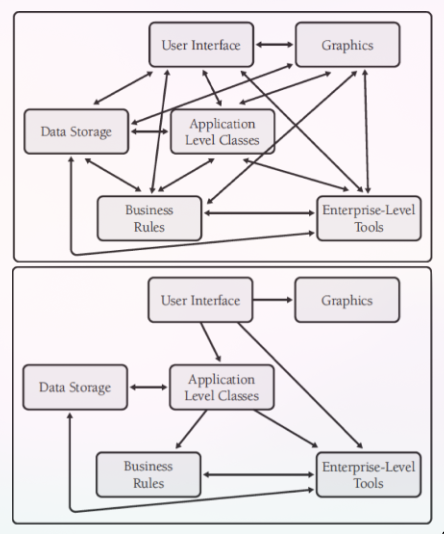
- Minimizing dependencies between components is important to create a loosely coupled architecture.
- By eliminating unnecessary dependencies, changes are localized and don’t propagate through the system.
- It is necessary to decide about how the components communicate data and control information.
Coupling
Skeletons
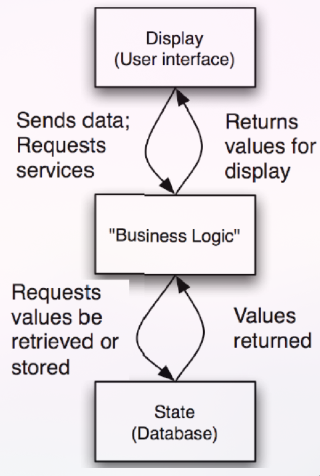
- A 3-tier software architecture enables IT systems to localize changes and handle transactional loads.
- A cooperating-processes architecture is well suited to operating systems because it isolates faults.
- It is probable that a distributed VOIP network (e.g., Skype) uses a peer-to-peer architecture.
Quality attributes
- Developers must pay attention to functionality, but a system has also quality attributes.
- A system’s architecture enables or inhibits qualities such as security or performance.
- Functional requirements that change are a challenge, but evolving quality attributes can force drastic changes.
- Example: a system to support 100 users may be impossible to scale up to 100,000 without a drastic architectural change.
- Architecture is likely to require more attention in systems with large scale or high complexity.
- When the system is simple, its architecture is unlikely to sink the project, so one pays little attention to it.
- There is no such thing as an inherently good or bad architecture.
- An architecture is more or less fit for some purpose.
- Architectures can be evaluated but only in the context of specific stated goals.
Architecture is orthogonal to functionality
- Architecture and functionality can be balanced.
- Architecture is mostly orthogonal to the system’s functionality.
- There is no single best architecture, but architectures are more suited to some tasks than others.
- A system’s architecture can be changed, but yet keeping its functionality
- The same architecture can be used on a system with different functionality.
- A poor architecture choice can make functionality and quality attributes difficult to achieve.
What makes a good architecture?
- The architecture should be the product of a small group of architects with an identified leader (avoid “design by committee” anti-pattern).
- The architect should base the architecture on a prioritized list of quality attributes.
- The architecture should be documented using views.
- The views should address the concerns of the most important stakeholders.
- The architecture should be evaluated for its ability to deliver the system’s important quality attributes.
- The architecture should lend itself to incremental implementation.
Presumptive Architectures
A presumptive architecture is a family of architectures that dominates a particular domain.
- Developers in that domain may have to justify a choice that differs from the presumptive architecture.
- Presumptive architectures are similar to reference architectures.
- A reference architecture is a family of architectures that describes an architectural solution to a problem.
- Presumptive architectures succeed because they are a good match for the common risks in the domain.
- IT developers who use the presumptive N-tier architecture will almost always do fine.
SUMMARY T7
- There is no single correct way to do software architecture.
- Architecture is mostly orthogonal to the system’s functionality.
- There is no single best architecture.
- There is no such thing as an inherently good or bad architecture.
- The architecture should be the product of a small group of architects with an identified leader
T8
Failure
The concept of failure is central to the design process, and it is by thinking in terms of obviating failure that successful designs are achieved.
- Avoiding failure is central to all engineering.
- One can use architecture techniques to mitigate the risks.
- Developers discard the designs that are predestined to fail and prefer those with low risk of failure.
- Building successful software means anticipating possible failures.
- No up-front design: just write code
- Use a yardstick: spend 10% of the time on design
- Build a documentation package
- ad hoc: decide on the spot what to do
Risk-Driven Approach
- The risk-driven approach help developers to build quality software quickly and at low cost.
- Architects have more architecture techniques than they can afford to apply.
- The risk-driven approach helps answer two questions:
- how much software architecture work should be done?
- which techniques should be used?
- The risk-driven approach guides architects to apply a minimal set of architecture techniques to reduce their most pressing risks
- Different developers perceive risks differently.
- They choose different techniques.
- The risk-driven model has the useful property that it yields arguments that can be evaluated.
- Example argument: We identified A, B, and C as risks, with B being primary. We spent time applying techniques X and Y because we believed they would help us reduce the risk of B. We evaluated the resulting design and decided that we had sufficiently mitigated the risk of B, so we proceeded on to coding
- identify and prioritize risks
- select and apply a set of techniques
- evaluate risk reduction
- waste time on low-impact techniques
- ignore project-threatening risks
- build quality systems by taking a path that spends their time most effectively
- address risks by applying design techniques, only when they are motivated by risks
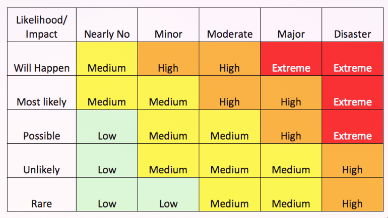
Risk = Failure x Impact
- In engineering, risk is commonly defined as the chance of failure multiplied by the impact of that failure: risk = probability of failure x impact
- The probability of failure and the impact are not certain, since they are difficult to measure precisely.
- A risk can exist (i.e., one can perceive it) even if its consequences do not materialize.
- A risk can be stated categorically, often as the lack of a needed quality attribute.
- It is better to describe risks such that one can later test if they have been mitigated.
Kinds of risks
- Describe each risk of failure as a testable failure scenario.
- Example: “During peak loads, customers experience user interface latencies greater than five seconds”.
- Projects face many different kinds of risks. Each pays attention to the risks of his/her specialty.
- Misunderstood quality attributes are a common risk.
| project management risks | software engineering risks |
|---|---|
| lead developer hit by bus | the server may not scale to 800 users |
| customer needs not understood | parsing of the alert messages are buggy |
| VP hates the product owner | the system is working now, but if we change anything it may collapse |
Prototypical risks
| project domain | prototypical risks |
|---|---|
| IT | complex, poorly understood problem unsure the real problem is being solved integration with existing software domain knowledge scattered modifiability |
| Systems | performance, reliability, security concurrency composition |
| Web | security scalability developer productivity / expressibility |
Risk Prioritisation
- Not all risks are equal, so they can be prioritized.
- Most teams prioritize risks by discussing the priorities amongst themselves.
- The team’s perception of risks may not be the same as the stakeholders’ one.
- Some technical risks, such as platform choices, may not be easily assessed by the stakeholders.
- Risks can be categorized on two dimensions:
- their priority to stakeholders (business)
- their perceived difficulty by developers (engineering)
Risk Mitigation
- Once one identifies the risks, some techniques can be applied to reduce their impact.
- Techniques go from pure analyses (calculate stresses) to pure solutions (flying buttress on churches).
Risk Techniques
| software engineering | other engineering fields |
|---|---|
| 1. design patterns | 6. stress calculation |
| 2. domain modelling | 7. breaking point testing |
| 3. throughput modeling | 8. thermal analysis |
| 4. security analysis | 9. reliability testing |
| 5. prototyping | 10. prototyping |
- One needs to be able to explicitly state how to choose techniques in response to risks.
- Create a handbook with entries: if we have <\a risk>, consider <\a technique> to reduce it
- A particular technique is good at reducing some risks but not others.
- Ideally, there would be a single technique to address every known risk.
- Some risks can be mitigated by multiple techniques, while other risks require techniques to be invented on the fly
Effort proporcional to risks
The risk-driven approach uses this principle: architecture efforts should be proportional with the risk of failure
- Whenever developers are unconcerned about security risks, they spend no time on security design.
- When performance is a critical risk, it should be addressed until an acceptable level is reached.
- When one applies the risk-driven approach, one only designs the areas where failure risks are perceived.
- Often, applying a design technique means building a model of some kind.
The effort spent on designing the architecture should be commensurate with the risks faced by the project.
- The architecture model will be detailed in some areas and sketchy, or even non-existent, in others.
- Models are an intermediate product.
- One can stop working on the models once he is convinced that the architecture is suitable for addressing the risks.
- The risk-driven approach facilitates the decisions, but it cannot make judgments.
- It identifies prioritized risks and corresponding techniques and guides on asking the right questions about the design work.
Styles of design
The risk-driven approach is compatible with the three design styles. All of these design styles agree that design should happen at some point.
- In BDUF, that time is up-front.
- In NDUF, it means doing architecture design during development, whenever a risk looms sufficiently large.
- Applying it to LDUF is a combination of the other two.
1. Evolutionary design (No DUF - NDUF)
- In evolutionary design, the design of the system grows as the system is implemented.
- Recent trends in software processes address most of the shortcomings of evolutionary design.
- Agile practices work against the chaos:
- refactoring cleans up the uncoordinated local designs
- test-driven development ensures that changes to the system do not cause it to lose or break existing functionality
- continuous integration provides the entire team with the same codebase
2. Planned design (Big DUF - BDUF)
- In planned design, architecture is detailed before construction.
- Analogies with bridges are used, since bridge construction rarely begins before the design is ended.
- Few people advocate doing planned design for an entire software system.
- Planned architecture design is useful when many teams working in parallel share an architecture.
- Even in planned design, an architecture should rarely be 100% complete before prototyping or coding.
- The design can be perfected with feedback from code.
3. Minimal planned design (Enough DUF - EDUF / Little DUF - LDUF)
- An hybrid style is minimal planned design.
- One can balance planned and evolutionary design.
- One way is to do some initial planned design to ensure that the architecture handles the biggest risks.
- Future changes to requirements can be handled through local design, or with evolutionary design.
- The idea is to perform architecture-focused design to set up an architecture that handles the biggest risks.
- One has more freedom in other design decisions
SUMMARY T8
- The risk-driven approach guides developers to apply a minimal set of architecture techniques to reduce their most pressing risks.
- Architecture efforts should be proportional with the risk of failure.
- One can stop working on the models once the architecture is suitable for addressing the risks.
- Few people advocate doing planned design (BDUF) for an entire software system.
T9
Tactics
- Architects need techniques to achieve particular qualities.
- The quality requirements specify the responses of the software system to realize business goals.
- Tactics are used by the architect to create a design.
- Tactics connect quality attribute requirements with architectural decisions.
A tactic is a design decision that impacts on specific quality attributes.
- A system design consists of a collection of decisions.
- Some of these decisions help control the quality attribute responses.
- Others ensure achievement of system functionality.
- Each tactic is a design option for the architect.
- For example, one tactic can introduce redundancy to increase the availability of a system. This is one possible option, among many, for the architect to increase availability.

- availability tactics
- modifiability tactics
- performance tactics
- security tactics
- testability tactics
- usability tactics
Availability
Availability quantifies the percentage of time during which a given system is operational and working correctly.
- It is an important aspect that has ramifications in other issues: confidence of the users in the products that they use, value of the information, processes efficiency, productivity of the organisations.
- Availability is normally measured by the MTBF (mean time between failures) and MTTR (mean time to repair). How? Easy:
- A failure occurs when the system no longer delivers a service that is consistent with its specification.
- This failure is observable by the users.
- A (combination of) fault(s) has the potential to cause a failure.
- Recovery or repair is an important aspect of availability.
- Availability tactics aim to avoid faults from becoming failures or at least reduce the effects of the fault and make repair possible

-
Many of the tactics are available within standard execution environments such as operating systems, application servers, and database management systems.
-
All approaches to addressing availability involve some type of:
- redundancy
- health monitoring to detect a failure,
- recovery when a failure is detected.
-
The monitoring or recovery is either automatic or manual
Fault detection
- Ping/echo: One component issues a ping and expects to receive back an echo from the component under scrutiny. It can be used by clients to ensure that a server object and the communication path to the server are operating.
- Heartbeat: One component emits a heartbeat message periodically and another component listens for it. If the heartbeat fails, the originating component is assumed to have failed and a fault correction component is notified.
- Exceptions: One method for detecting faults is to encounter an exception, which is raised when one of the fault classes is recognized.
Fault recovery
- Voting: Processes running on redundant processors each take the input and compute the output that is sent to a voter. Popular voting algorithm are “majority rules” or “preferred component”. Voting is used to correct faulty operation of algorithms or failure of a processor.
- Active redundancy: All redundant components respond to events in parallel. The response from only one component is used (usually the first to respond); the rest are discarded.
- Passive redundancy: One component (the primary) responds to events and informs the other components (the standbys) of state updates they must make. When a fault occurs, the system must first ensure that the backup state is sufficiently fresh before resuming services.
Fault prevention
- Removal from service: This tactic removes a component from operation to undergo activities that prevent failures. Example: rebooting a component to prevent memory leaks to cause a failure.
- Transactions: A transaction is the bundling of several sequential steps such that the bundle can be undone at once. Transactions are used to prevent any data from being affected if one step in a process fails. They also prevent collisions among several simultaneous threads accessing the same data.
- Process monitor: Once a fault in a process has been detected, a monitoring process can delete the nonperforming process. A new instance of the process needs to be created.
Performance
Performance refers to the capacity of a system to respond to its stimulus, that is, the time necessary for responding to the events or the number of events processed by time unit.
- Google loses 20% traffic if their web sites respond 500 ms slower than usual.
- Amazon loses 1% of revenue for every 100 ms in latency.
- A Mozilla study shows that if the webpage is not loaded within 1 to 5 seconds, users will leave it.
Events
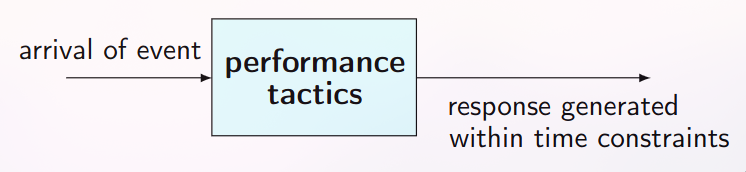
- Performance tactics generate a response to an event arriving at the system within some time constraint. The event can be single or a stream and is the trigger for a request to perform computation.
- It can be the arrival of a message, the expiration of a time interval, the change of state in the system environment, etc.
- The system processes the events and generates a response.
- Performance tactics control the time within which a response is generated.
The time between the arrival of an event and the generation of a response to it.
Resource consumption and blocked time
- After an event arrives, either the system is processing on that event or the processing is blocked for some reason.
- Resource consumption: Resources (CPU, data stores, network bandwidth, memory, and buffers) must be managed.
- Access to critical sections must be made sequential.
- All the phases to process an event contribute to the overall latency of the processing of that event.
- Blocked time: A computation can be blocked from using a resource due to its contention or unavailability.
- resource demand
- resource management
- resource arbitration
1. Resource demand
- Event streams are the source of resource demand.
- Two main aspects in resource demand are:
- The time between events in a resource stream
- How much of a resource is consumed by each request
- One tactic to decrease latency is to reduce the resources required for processing an event stream.
- Increase computational efficiency: One step in the processing of an event is applying some algorithm.
- Improving the algorithms decreases latency.
- Sometimes one resource can be traded for another. For example, data may be kept in a local/fast repository to avoid getting it from a slow resource.
- Reduce computational overhead: If there is no request for a resource, processing needs are reduced.
- The use of intermediaries (important for modifiability) increases the resources consumed in processing an event stream, and so removing them improves latency. It is a modifiability/performance tradeoff, however.

- Another tactic for reducing latency is to reduce the number of events processed.
- Manage event rate: If one can reduce the sampling frequency at which variables are monitored, demand can be decreased. This is often possible if the system was overengineered.
- Control frequency of sampling: If the arrival of externally generated events is not controlled, queued requests can be sampled at a lower frequency, possibly resulting in the loss of requests.
2. Resource management
- Introduce concurrency: If requests can be processed in parallel, the blocked time can be reduced.
- Concurrency can be introduced by processing different streams of events on different threads.
- Appropriately allocating the threads to resources (load balancing) is important to maximally exploit the concurrency.
- Maintain multiple copies of either data or computations: Clients in a client-server pattern are replicas of the computation. The purpose of replicas is to reduce the contention that would occur if all computations took place on a central server.
- Caching is a tactic to reduce contention, in which data is replicated, either on different speed repositories or on separate repositories. Since the cache data is a copy of existing data, it is relevant to keep the copies consistent and synchronized.
- Increase available resources: Faster processors, additional processors, additional memory, and faster networks all have the potential for reducing latency.
- Cost is usually a consideration in the choice of resources.
- This is a cost/performance tradeoff.
How to get ideal performance
| Resource demand | Resource Management | Resource arbitration |
|---|---|---|
| Increase computation efficiency | Introduce concurrency | Scheduling policy |
| Reduce computational overhead | Maintain multiple copies (redundancy) | |
| Manage event rate | Increase avaliable resources | |
| Control Frequenct of sampling |
SUMMARY T9
- Tactics are used by the architect to create a design.
- A tactic is a design decision that impacts on specific quality attributes.
- There are tactics for availability, modifiability, performance, security, testability, and usability.
- Availability tactics try to keep faults from becoming failures or at least reduce the effects of the fault and make repair possible.
- Performance tactics generate a response to an event arriving at the system within some time constraint.
T10
Patterns
Each pattern describes a problem that occurs over and over again in our environment and then describes the core of the solution to that problem in such a way that you can use this solution a million times over without ever doing it the same way twice.
thus
A textual description of a generic solution for a recurring problem in a given context
- a reusable solution to a recurring problem
- a pre-designed chunk, tailored to fit a given situation
- a package of design decisions that can be reused as a set
- system patterns (architectural styles)
- design patterns
- code patterns
- They are not perfect for every problem
- Their ability to separate the things that change from that which does not is useful for implementing systems
- Creational
- Structural
- Behavioural
- strategy (structural)
- observer (behavioural)
- decorator (structural)
T11
Architectural style
- set of component types (e.g., process, procedure) that perform some function at runtime
- a topological layout of the components showing their runtime relationships
- a set of semantic constraints
- a set of connectors (e.g., data streams, sockets) that mediate communication among components
A system that conforms to a given style must use those types, which restricts the design space.
Constraints
- Constraints can act as guide rails that point a system where you want it to go.
- One can think of a style as a prefabricated set of constraints that can be reused.
- The consistency brought about by the constraints of the style can encourage clean evolution of the system, which can make maintenance easier.
- Communication among developers is improved since the simple name of a style conveys design intent.
Platonic vs. embodied
- A platonic architectural style is an idealization. One finds it in books and only rarely in source code.
- An embodied architectural style exists in real systems. It often violates the strict constraints found in platonic styles. Example: the platonic client-server style requires that servers be unaware of clients.
- One may find embodied versions of the style where servers occasionally push data to the clients. Depending on how this is implemented, it may result in a server that depends on the clients.
Styles
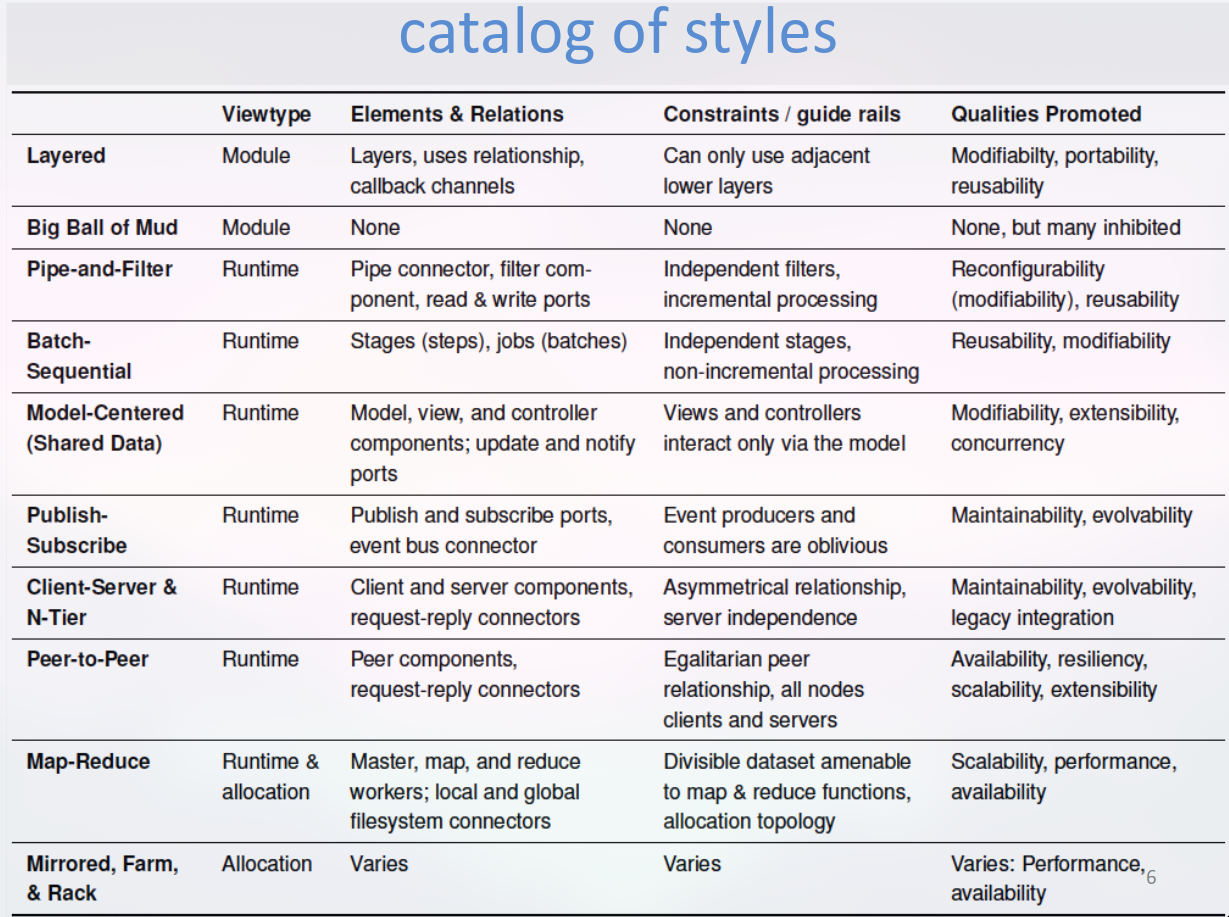
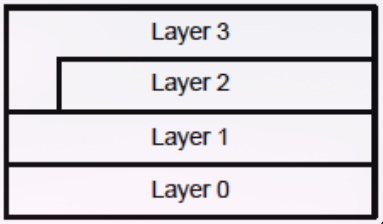
1. Layered style
- The essential element of the layered style is a layer.
- The essential relationship is a uses relationship, a specialization of a dependency relationship.
- The layered style consists of a stack of layers.
- Each layer acts as a virtual machine for the layers above it and their ordering forms a DAG.
- In a simple layered style, a layer can use only the layer directly beneath it.
- Quality attributes promoted: modifiability, portability, and reusability.
- The layered style can vary greatly from its platonic form to its embodied form.
- In practice a layered style may violate its constraint
- You may see skipping of layers or lower layers using upper layers.
- Lower layers can safely communicate with higher layers if they use a callback mechanism.
- “Lasagna code” refers to a program structure that follows the layered style.
2. Big Ball of Mud style
- It has no evident structure.
- Promiscuous sharing of information is typical, to the extent that data structures become effectively global.
- Repairs and maintenance are expedient and resemble crude patches rather than elegant refactorings.
- No effort is made to enforce any conceptual integrity or consistency (“spaghetti code”).
- Such systems have poor maintainability and extensibility.
- This style is a good enough strategy of engineering.
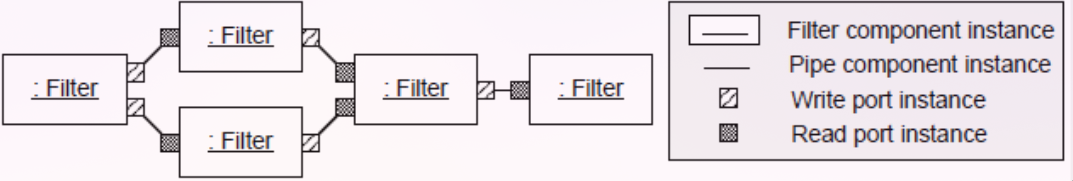
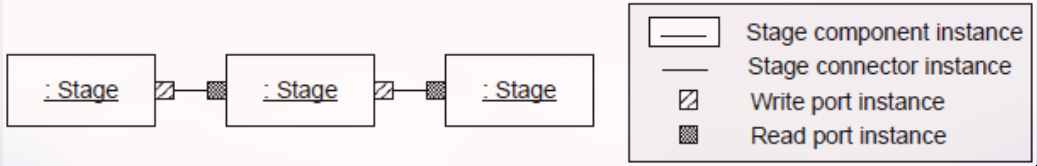
3. Pipe and filter style
- Data flows through pipes to filters that work on the data.
- The pipe-and-filter network is continually and incrementally processing data.
- The pipe-and-filter style consist of four elements: pipes, filters, read ports, and write ports.
- A filter reads input from the input ports, does some processing, and writes output to the output ports.
- It repeats this until it is time to stop.
- Filters can enrich, refine or transform the data
- Each filter applies a function to its input.
- Pipes must only transport the data in one direction, without changes, and in order.
- Loops in the network are rare and often prohibited.
- Filters may not interact with each other, even indirectly, except through pipes.
- Filters cannot share state with each other.
- A filter incrementally reads the input and, as it processes that input, incrementally write its output
4. Batch-sequential style
- Data flows from stage to stage.
- Each stage completes all of its processing before it writes its output.
- Data can flow between stages in a stream but is more often written to a file on disk.
- It has similar constraints to the pipe-and-filter style.
- Each stage is similarly independent.
- A stage depends on the data that it takes in.
- Stages do not interact with each other except through the input and output streams or files.
- Both Batch-sequential style as well as Pipe and filter style decompose the task into a fixed sequence of computations, interacting only through data.
Batch-sequential vs Pipe and filter
| Batch Sequential | Pipe and filter |
|---|---|
| - Coarse-grained - High latency - External access to input - No concurrency - No interaction |
- Fine-grained - Results start processing - Localized input - Concurrency possible - Interaction possible |
5. Model-centered style
- Independent components interact with a central model (data store) instead of with each other.
- Every model-centered system has a model component and several view, controller, or view-controller components.
- This style is related to several design patterns, including the document-view, MVC, and observer.
- Views and controllers depend only on the model, not on each other.
- Modifiability is enhanced because the producer and consumer of information are decoupled.
- The system is extensible since unanticipated views and controllers are easily added.
- It can be easier to manage and persist state, since it is centralized in the model component.
- Concurrency may be promoted since views and controllers can run in their own threads or processes.
- This style is useful when one does not know the future configuration of the system.
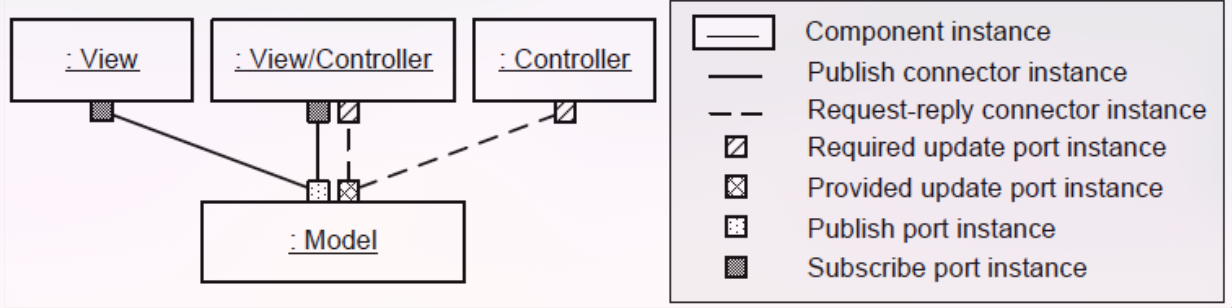
6. Publish-subscribe style
- Independent components publish events and subscribe to them.
- A publishing component is ignorant of the main reason why an event is published.
- A subscribing component does not know why or who published the event.
- This style defines publish and subscribe ports, and one connector (an event bus connector).
- Any kind of component can publish (subscribe) events as long as it uses a publish (subscribe) port.
- One component can publish an event and many components can subscribe to it.
- The event bus connector delivers events:
- publishers trust that events are delivered to subscribers
- subscribers trust that they receive events they subscribe to
- Producers and consumers of events are decoupled.
- The system is more maintainable and evolvable.

7. Client-server style & N-tier
- Clients synchronously request services from servers.
- The client can request that the server do the work.
- Communication is initiated by clients, not the server
- The server does not know the identity of the client until it is contacted.
- Clients must either know the identity of the server or know how to look up the server.
- The client-server style has several variation points:
- connectors may be synchronous or asynchronous
- there may be limits on the number of clients or servers
- connections may be stateless or stateful (i.e., sessions)
- the system topology can be static or dynamic
- Another variant is the N-tier style
- It uses two or more instances of the client-server style to form a series of tiers
- Requests must flow in a single direction
- A common case is a 3-tier system where:
- a user interface tier acts as a client for the business logic tier server
- business logic tier server acts as a client for the persistence tier server
- Tiers have exclusive functional responsibilities.
- The user interface tier is exclusively responsible for user interaction
- The persistence tier exclusively saves persistent data
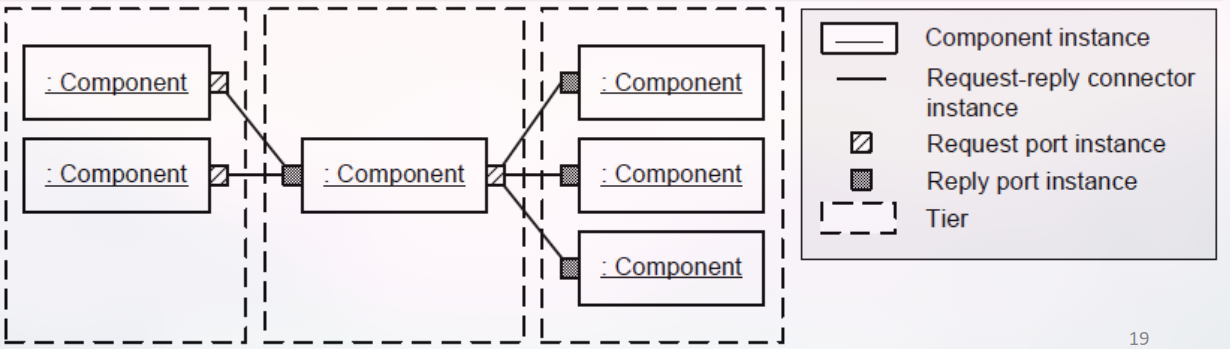
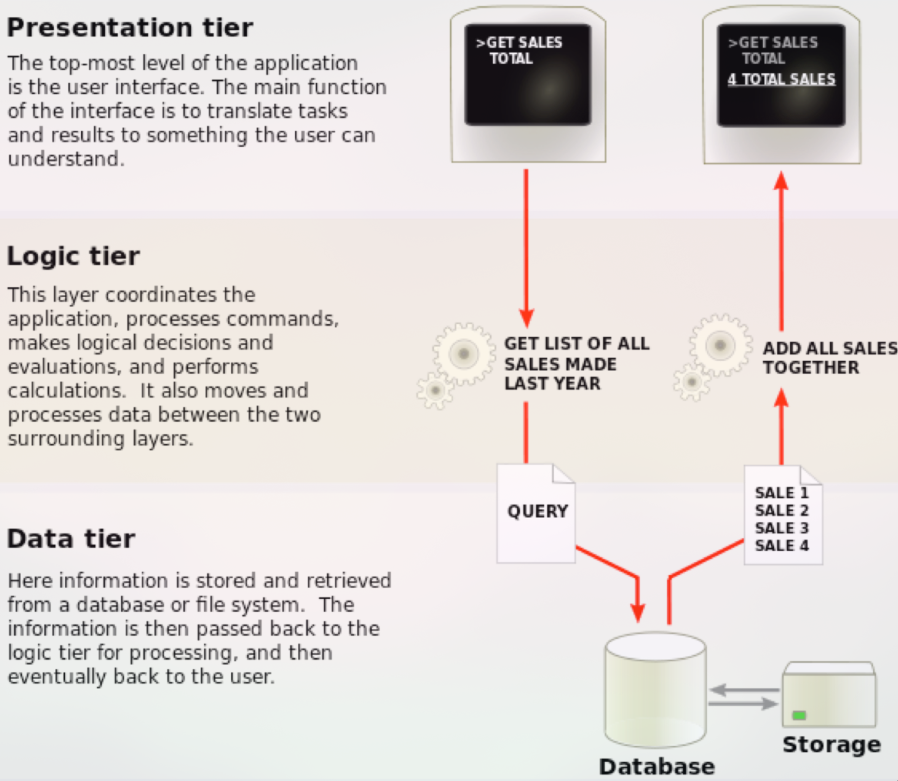
8. Peer-to-peer style
- Nodes communicate with each other as peers.
- Hierarchical relationships are prohibited.
- Each node has the ability, but not obligation, to act both as a client and as a server.
- The result is a network of nodes operating as peers.
- A node can request or provide services to any node.
- The elements of the peer-to-peer style are similar to those of the client-server style.
- A peer-to-peer connector has identical roles on either end allowing both requests and responses.
- A peer-to-peer system is egalitarian where the client-server style is hierarchical.
9. Map-reduce style
- This style is appropriate for processing large datasets (search engines and social networking sites)
- Simple programs (sorting or search) execute slowly on large datasets, if a single computer is used.
- This style enables the computation to be spread across multiple computers.
- As the number of computers used increases, the likelihood that one of them will fail also increases.
- This style enables recovery from such failures
10. Mirrored, rack, and farm style
- The previous architectural styles have been from the module and runtime viewtypes
- The styles from the allocation viewtype are more likely to be discussed by network engineers than software architects